
£3 million Grants for Aspiring Innovation Leaders
UKRI Future Leaders Fellowships competition supports early-career innovators with up to seven years of funding and other resources.
Our latest insights on government, debt, equity funding, and UK innovation.

UKRI Future Leaders Fellowships competition supports early-career innovators with up to seven years of funding and other resources.

Companies in England can secure up to £80,000 in grant funding for on-farm demonstration projects.

Innovate UK is offering substantial grants to agriculture and food technology companies in North and Mid Wales.

Find grants for your innovative startup or scaleup with the latest edition of Grants Watch.
Won an EU grant? The EIC Transition scheme is a great opportunity to secure further funding for your game-changing technology.

Find out if you could secure a game-changing grant from the EU-funded EIC Pathfinder competition.

Find out if you’re eligible for this unique grant-investment hybrid opportunity from Innovate UK.

Finished a grant-funded project and need capital to take your technology to market? An Innovation Loan may be the answer.

Find out if your UK startup or scaleup can apply for up to €2.5 million in grant funding from the EIC Accelerator scheme.

Find out if you could secure a large grant from the National Institute for Health and Care Research.

The key things you need to know about the new claim notification form for R&D Tax Relief claims.

GrantTree CEO Bob Leung explains what we learned from our radical self-set pay model and why we moved to a more traditional system.

Your guide to the main R&D Tax changes impacting your company this year.

Looking to claim R&D Tax Relief on subcontracted R&D? Read this before you file.
Most payments for overseas contractors and externally provided workers no longer qualify for R&D Tax Relief.

The key things you need to know about the July 2024 round of Innovate UK’s Smart competition including who’s eligible and how to apply.

Secure up to £1 million to turn your bio-based manufacturing idea into a commercial reality.

The major announcements from the 2024 Autumn Budget impacting innovative UK companies.

The key things you need to know about Enhanced R&D intensive support, offering government funding to innovative, unprofitable SMEs.

Find out if you’re eligible for up to £3 million in grant funding for your quantum computing project.

Senior R&D Technical Consultant Emily Siddaway-Parmenter discusses her career to date and her work supporting other female engineers.

Dramatic drop in non-compliance shows HMRC’s compliance crackdown is working, though some of its tactics remain controversial.

Expert tips for using the IFS Portal for Innovate UK grants. Successfully navigate your application, project setup, and mid-project reporting.
The R&D claim deadline is two years after the end of the accounting period in which your R&D took place. Here’s what you need to know.

Inclusion of cloud and data costs in list of qualifying expenditures means extra capital for companies working on AI-related projects.

New joiners add considerable claim experience and technical acumen to GrantTree’s R&D Tax offering.
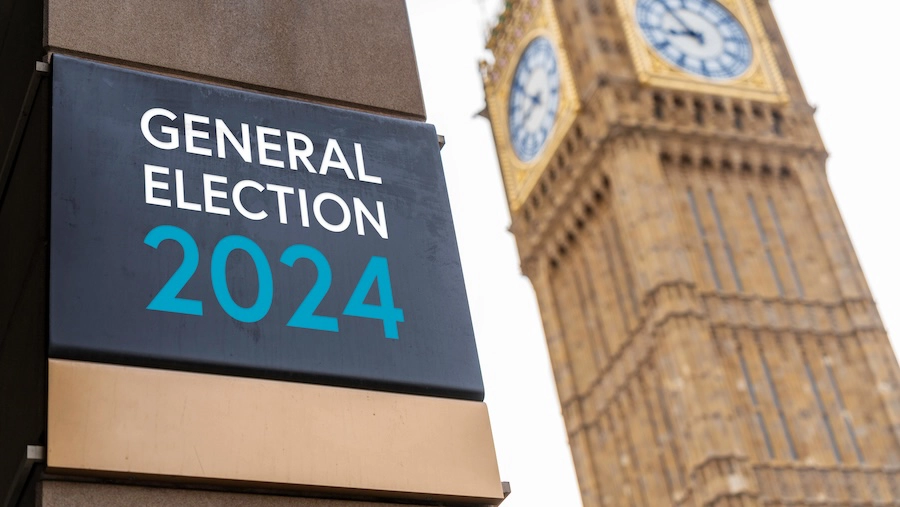
Pre-election promises bring welcome relief to business leaders worried about remaining compliant with further reforms.

Innovate UK is offering up to £50,000 to help small businesses in West Yorkshire develop innovative health technology solutions.

Technical reports are about to become mandatory for all R&D Tax claimants. Here are my insider tips for making sure yours passes muster with HMRC’s inspectors.

Rishi Sunak’s unexpected announcement will also have consequences for companies hoping to apply for grant funding. Here’s how.
Keep up to date with all things GrantTree. You will receive a newsletter once a month containing tailored news, insights and white papers.

We are GrantTree. And we are here to make innovating easier. Our specialists will connect you with the funding you need so you can focus on growing your business.
© Copyright. GrantTree. CN 07403467. VAT GB 101974824. All Rights Reserved.